The “Made Easy” Compliance Solution for Any Cyber Regulation
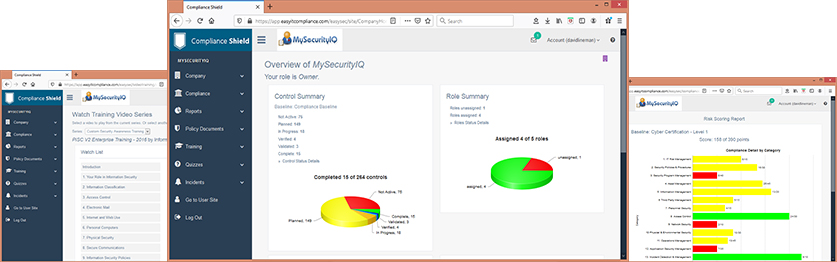
Information Shield has taken our “Made Easy” security policy library to the next level with ComplianceShield. ComplianceShield helps automate all aspects of cyber security governance. Pre-loaded with Control Baselines and Security Policy Templates, it has everything you need in one integrated platform.
Streamline Compliance with these Frameworks:
FTC Safeguards Compliance (NADA)

NYS-DFS Compliance Automation
Key ComplianceShield Features Compliance Automation
Use our Common Control Library (CCL) to quickly build a cyber security program to comply with all common regulations and frameworks,
Develop Information Security Policies
Create security policies in minute with our ISO 27002 policy template library. Over 50 policies, procedures and plans than can easily be customized.
Measure and Track User Acknowledgement
Customized “User Portal” enables you to easily distribute security policies, training and assessments to employees and contractors. Validate user understanding and formal acknowledgement of security policies.
Assess and Manage Third Party Vendors
ComplianceShield supports a complete Vendor Risk Management process using our Common Vendor Assessments. Easily create and distribute Cyber Risk Assessments to vendors and track results.
Educate and Train Users
Educate users with built-in security awareness training. Customized “User Portal” enables you to easily distribute policies and training to employees and contractors.
Measure and Track Control Compliance
Measure and track compliance with Controls including evidence storage and sharing. Easily show management progress against compliance goals.
Manage Information Security Incidents
Report, track and manage information security incidents. Multiple custom incident types and routing to response teams. Supports built-in Incident Response Procedure.
Perform IT Risk Assessments
Educate users with built-in security awareness training. Customized “User Portal” enables you to easily distribute policies and training to employees and contractors.
Define the Information Security Organization
Measure and track compliance with Controls including evidence storage and sharing. Easily show management progress against compliance goals.
Manage Ongoing Compliance
Report, track and manage information security incidents. Multiple custom incident types and routing to response teams. Supports built-in Incident Response Procedure.
Have questions about building a cyber program that works?
Call us now for a FREE 30 minute phone consultation with a cyber expert. 888-641-0500








